A new cyber threat, coined a “Black Storm” attack, could potentially wreak havoc on communications service provider (CSP) networks. While DDoS amplification attacks rely on DNS servers or other similar open services to interrupt connectivity, a Black Storm attack can leverage any device connected to the Internet. Researchers caution that the volume from one Black Storm attack could terminate medium to large-sized enterprises in a clean sweep and severely cripple a large-scale CSP network.
The potential devastation of Black Storm attacks on CSP networks
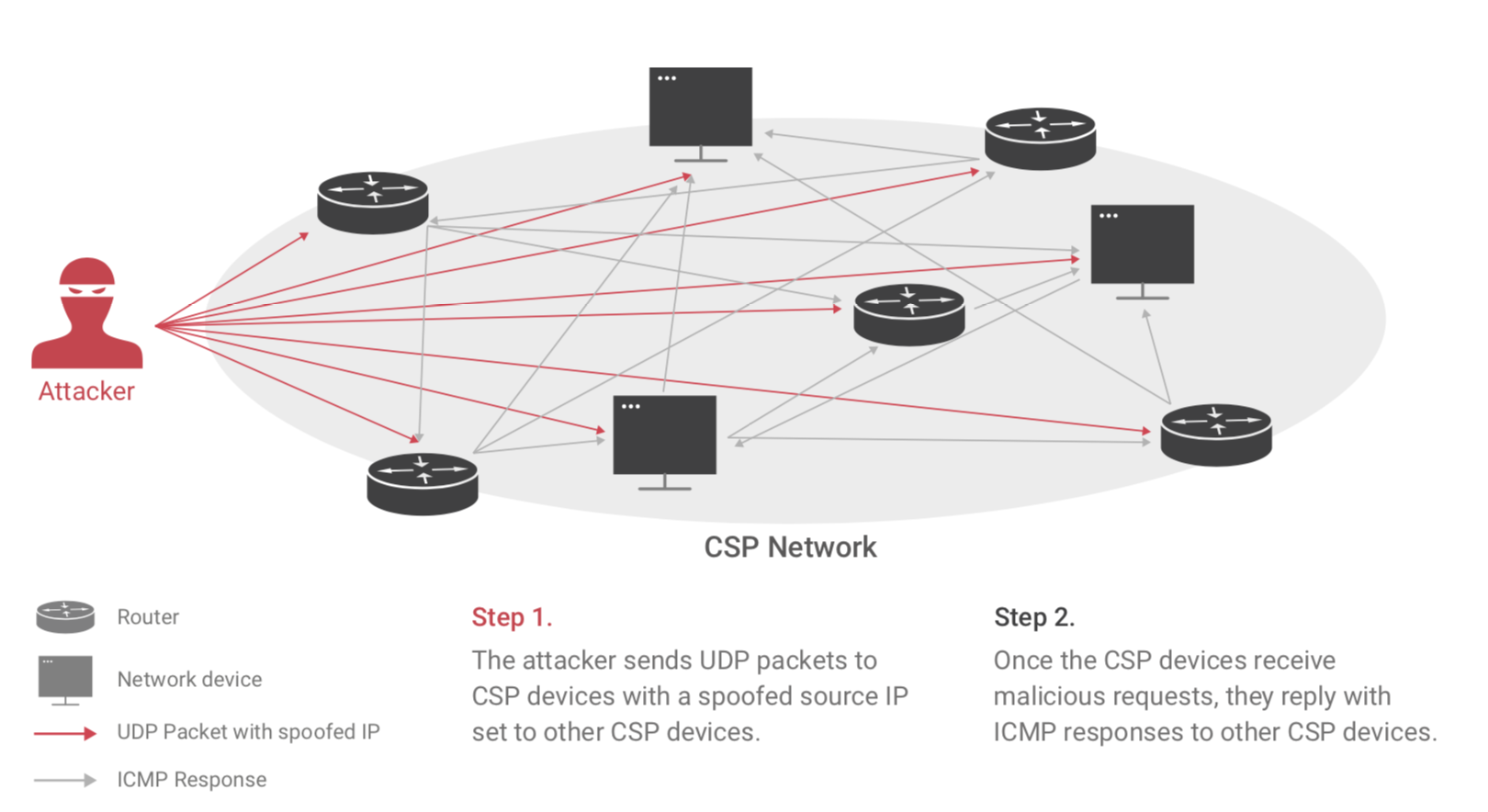
Hackers can achieve Black Storm attacks more easily than amplification attacks, which could quickly dominate the cyberworld. Black Storm attacks could be manifested by hackers employing a BlackNurse attack in a reflective manner (rBlackNurse attacks). By generating spoofed UDP requests to CSP devices’ closed UDP ports—a reflection of the ping replies returned to the CSP network ping sources in BlackNurse attacks—the devices respond with destination port unreachable responses. As more devices continue to respond to the spoofed IP source, the volume of responses completely overwhelms the target CSP network and creates the Black Storm attack.
We advises CSPs to perform regular vulnerability scanning, apply access control to routers and use deep learning-based detection methods. Deep learning approaches can help CSPs analyze huge amounts of data quickly and accurately while overcoming the inefficiencies inherent in threshold or signature-based methods.
