May 27, 2020
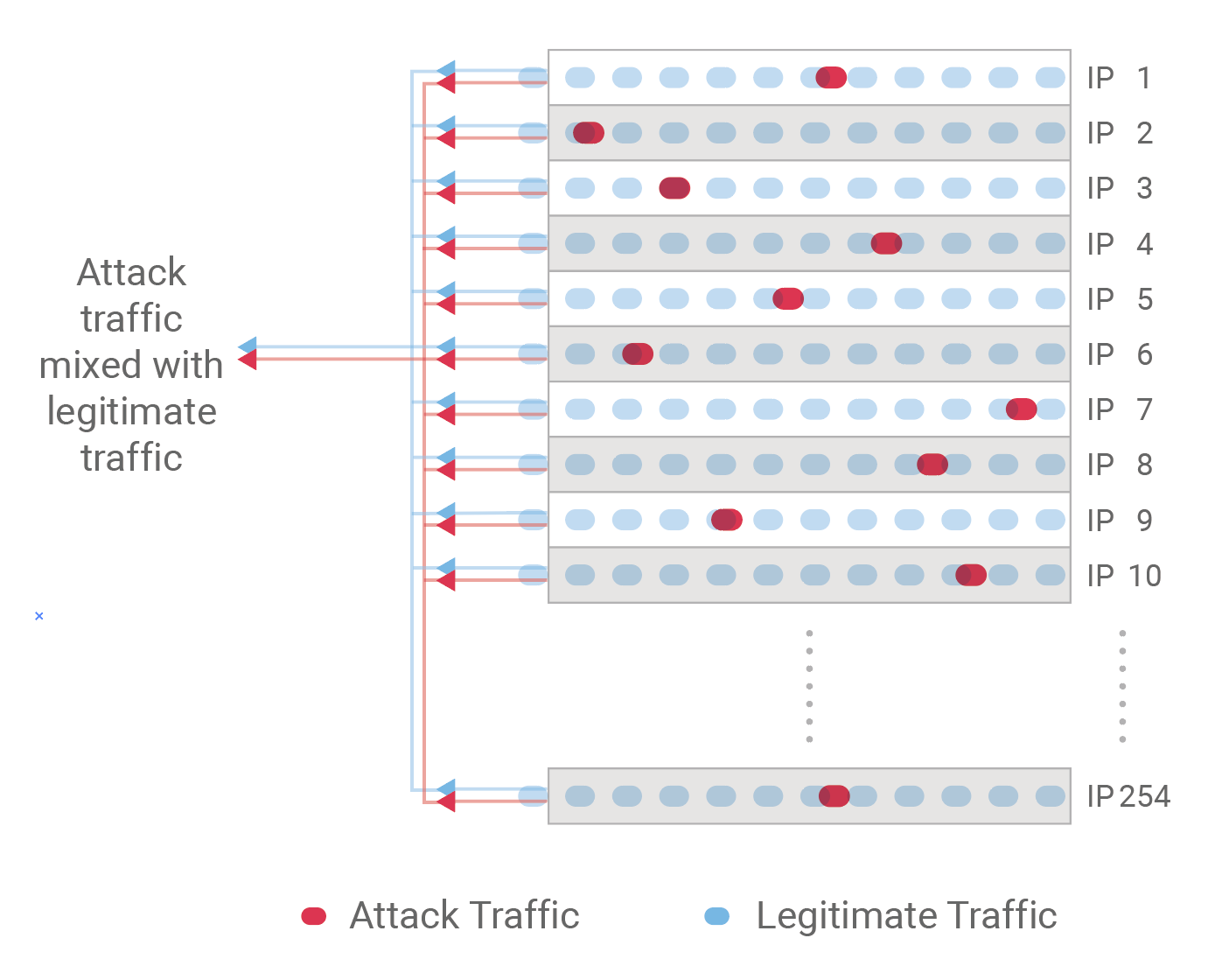
Nexusguard Research identified a new breed of stealthy DDoS attacks known as Bit-and-Piece attacks that target ASN-level CSP networks by dispersing small pieces of junk traffic across a diverse pool of IP addresses across hundreds of IP prefixes. This stealthy tactic is designed to evade detection. Going unnoticed, the convergence of polluted traffic toward the target IP prefix forms a massive traffic flow that can easily go beyond the capacity limits of generic mitigation devices, leading to a high latency at best, or deadlock at worst.
 Why is it difficult for telcos and ISPs to detect and mitigate this attack?
Why is it difficult for telcos and ISPs to detect and mitigate this attack?
Detection
Legacy flow-aware devices such as firewalls, load balancers, IPS, IDS, etc. often fail to detect stealthy
network layer attacks, which could become bottlenecks themselves.
Mitigation
When faced with powerful or advanced attacks such as Bit-and-Piece attacks, blackholing traffic to
targeted IP addresses as a mitigation measure is no longer effective nor is it viable.
Designed to protect large networks from L3/L4 attacks of all complexities, Nexusguard InfraProtect offers telcos and ISPs the ability to leverage Nexusguard's globally distributed infrastructure to be used as an off-site sandbox to perform traffic analysis, shaping and attack mitigation.
The multi-layered detection and mitigation engine features Network Behavior Analysis (NBA) to analyze traffic data in order to detect traffic anomalies and alerts the CSP to divert traffic to Nexusguard’s scrubbing cloud. Only clean traffic is forwarded back to the origin server.
.png)
To learn more about how to counter the threat from Bit-And-Piece Attacks, please read about Nexusguard’s Origin Protection.


